Bellflower Unified School District publicly identified a network security incident in August 2025 after phone and internet outages hit campuses, but the disruption appears to have received little independent media attention.
Bellflower Unified School District said an early August cybersecurity incident began after IT staff detected anomalous activity in its network environment, prompting the district to remediate systems, rebuild a secure network and restore operations. The district later said many network services were inoperable for a brief period, but it has since returned to full operations.
The district had publicly identified the problem as security-related by Aug. 5. In a staff update that day, Bellflower said internet and phone service had been down since Aug. 4 and that, “as a precautionary measure following a network security incident,” certain systems had been taken offline to protect the network. In separate public messages to families on Aug. 5, district officials said phone lines were down at the district office and all schools, then later said phone service had been restored. The district’s incident page later said the outage affected on-premises servers and not cloud-based databases.
By Aug. 8, the district told staff it had encountered technical issues in its network that included “isolated, unusual activity,” and said IT personnel and outside partners were working through internal security protocols to assess the scope of the problem. Staff were told to disconnect from wired ethernet, use a temporary guest network and remain cautious about suspicious links and attachments.
District officials said they retained an independent third-party forensic team, notified the FBI and the U.S. Department of Homeland Security, and implemented additional firewall, credential and other security policy changes while the review continued. The district said it had not found evidence of further anomalous activity.
Bellflower also said sensitive staff and student data is stored in separate externally hosted systems that were not impacted by the event, and by late September said it had no indication that sensitive student, parent or employee data was accessed or acquired. In an Oct. 30 update, however, the district said it was aware of an allegation that certain district data had been removed from the network environment, while continuing to say its assessment was ongoing. Bellflower did not publicly identify a threat actor or describe the incident as ransomware.
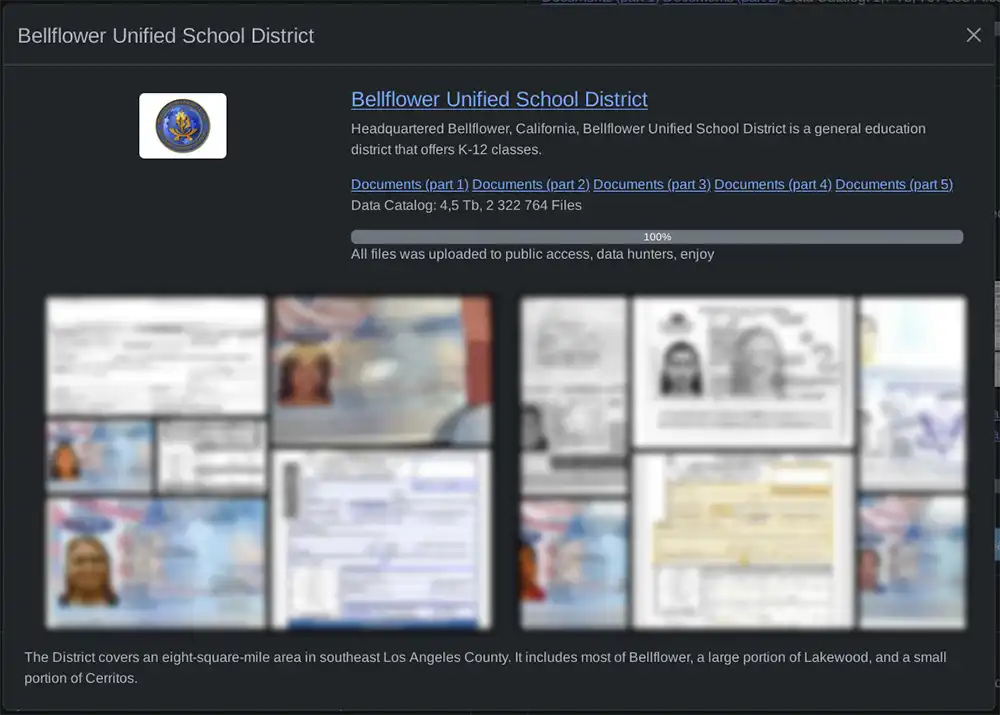
Leak-site trackers later recorded a claim by the Rhysida ransomware group against Bellflower Unified on Oct. 28, but that attribution has not been confirmed by the district or law enforcement and remains an unverified criminal claim.
The district issued follow-up notices dated Aug. 5, Aug. 8, Aug. 11, Aug. 18, Sept. 26 and Oct. 30, indicating the incident required months of updates even after internet access and core functionality were largely restored. On Aug. 11, Bellflower said all sites had internet access again, most functionality had been restored and passwords had been reset for security purposes.
Bellflower Unified publicly identified the incident as security-related within days and continued issuing updates as the review unfolded, but the case appears to have received little or no independent media coverage. That left much of the public record to the district’s own disclosures, with later leak-site tracking adding only an unconfirmed criminal claim.
Bellflower Unified serves about 10,000 students across 15 schools in southeastern Los Angeles County, according to district, state and federal education listings.












