West Pharmaceutical Services said a May 4 cyberattack disrupted global operations, with some shipping, receiving and manufacturing processes still being restored.
West supplies packaging and drug delivery products used by pharmaceutical and biotechnology companies, making any prolonged disruption a potential supply-chain concern. The Exton, Pennsylvania-based company says it has about 10,000 employees across 50 sites worldwide and ships about 43 billion components and devices annually.
West said it detected an intrusion May 4 and later determined the event was a cyberattack. In a May 7 notice, the company said it proactively took systems offline for containment, notified law enforcement and brought in outside cyber-forensic experts.
In a Form 8-K dated May 7 and signed May 11, West said the incident was a material cybersecurity attack in which an unauthorized party exfiltrated certain data and encrypted certain systems. The company said its investigation into the nature and scope of the incident remains ongoing, including the extent of data affected.
West said it engaged Palo Alto Networks’ Unit 42 to support its investigation, containment and recovery work. The company said core enterprise systems have been restored, and critical processes for shipping, receiving and manufacturing have restarted at some sites.
Restoration at remaining sites is still in progress, and West said it has not finalized a timeline for full restoration. The company said it is using business continuity plans and working with customers to reduce risk and minimize delays.
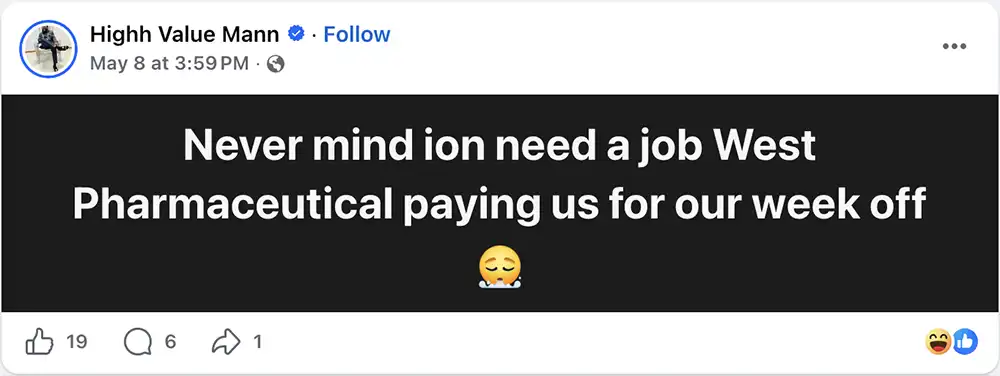
A public Facebook post from May 8 by a person identifying as a West worker suggested some employees were being paid during downtime. DysruptionHub could not independently verify the person’s employment status or the scope of any work stoppage.
A German local news report published Tuesday said West’s Eschweiler site was affected as part of the global disruption, with IT systems taken offline and operations interrupted there and at the company’s Nouvion-en-Thiérache site in France. The report said Eschweiler, where West makes elastomer products and employs about 1,200 workers, was in a controlled restart phase after core enterprise systems were restored. West has not identified affected sites by name in its U.S. disclosures.
West Pharmaceutical Services did not immediately respond to a DysruptionHub request for comment seeking more detail on the systems affected, the categories of data exfiltrated, site-level restoration status, employee downtime, any customer delivery impacts, whether a ransom demand was made and whether a threat actor has been identified.
West’s public location page lists its global headquarters in Exton and manufacturing, research, tooling, warehouse and distribution operations in several U.S. states, including Pennsylvania, Arizona, Florida, Indiana, Michigan, Nebraska, North Carolina and Puerto Rico.
The company has not publicly named a threat actor or confirmed a ransom demand. DysruptionHub could not independently confirm whether any leak-site claim is connected to the incident. The company did confirm data exfiltration and system encryption in its SEC filing.
West said the financial impact of the incident, if any, had not been determined at the time of filing. The company said its investigation and restoration work remained ongoing.
West’s disclosure follows cyber incidents at other medical technology companies where outages reached beyond back-office IT. Stryker said a March cyberattack disrupted order processing, manufacturing and shipping, while Masimo said a 2025 cyberattack affected manufacturing and order fulfillment. West has not said whether its incident delayed customer deliveries or affected patient-facing services.
West’s latest public update says core enterprise systems are restored, but some site-level shipping, receiving and manufacturing recovery remains in progress, with no finalized timeline for full restoration.











